Mastering AWS IAM Roles and Policies for Secure Cloud Architecture
IAM has become a complete mess with all the different policy types, permission boundaries, and evaluation rules flying around. As someone who has wrestled with AWS security for years across dozens of accounts, I learned everything there is to know about what actually works in practice. Let me share what I’ve picked up.
The Principle of Least Privilege
Every IAM policy should grant the minimum permissions necessary for whatever task you’re doing. Sounds simple, right? But it actually takes real discipline to implement. What usually happens is developers request broad permissions to avoid having to troubleshoot access errors, and gradually you end up with excessive privileges scattered across your organization.
Start by figuring out exactly what actions your applications and users actually need. Use CloudTrail to look at the real API calls being made by your existing principals. AWS Access Analyzer can even generate policies based on what it observes, which gives you a data-driven starting point for least privilege policies instead of just guessing.
And please, resist the temptation to just slap AdministratorAccess or PowerUserAccess on everything in production. Sure, they’re convenient when you’re developing, but these managed policies grant way more access than any single application actually needs. Take the time to create custom policies tailored to your specific use cases.
Understanding Policy Evaluation
AWS evaluates policies in a specific order that determines whether you get access or not. Honestly, I should have started here., because without understanding the evaluation logic you’ll be chasing your tail debugging access issues. By default, everything is denied. Explicit allows in identity-based or resource-based policies grant access. But here’s the catch – explicit denies in any policy always win over allows.
Permission boundaries add another layer to the whole thing. They set the maximum permissions an identity can have, regardless of what other policies say. I use permission boundaries when I want to delegate IAM administration safely. Teams can create their own roles and users, but only with permissions that the boundary allows.
Role-Based Access Patterns
Always prefer IAM roles over IAM users for workload access. Roles give you temporary credentials that rotate automatically, which means you don’t have the risk of long-lived access keys getting compromised. Your EC2 instances, Lambda functions, ECS tasks, and EKS pods should all be using roles for AWS API access.
You should implement role assumption for human access too. Instead of granting permissions directly to IAM users, create roles with specific permission sets. Users assume the appropriate role for whatever task they’re doing, which gives you way better audit trails and enables just-in-time access patterns.
Cross-Account Access
If you’re running multiple AWS accounts (and you probably should be), you need secure cross-account access patterns. Create roles in your destination accounts that trust your source accounts. Then principals in the source account can assume these roles to access resources in the destination. This approach keeps identity management centralized while maintaining account isolation.
Use external IDs when you’re letting third-party services assume roles in your account. The external ID prevents confused deputy attacks where bad actors trick legitimate services into accessing your stuff. Never share external IDs publicly and make sure to rotate them periodically.
Resource-Based Policies
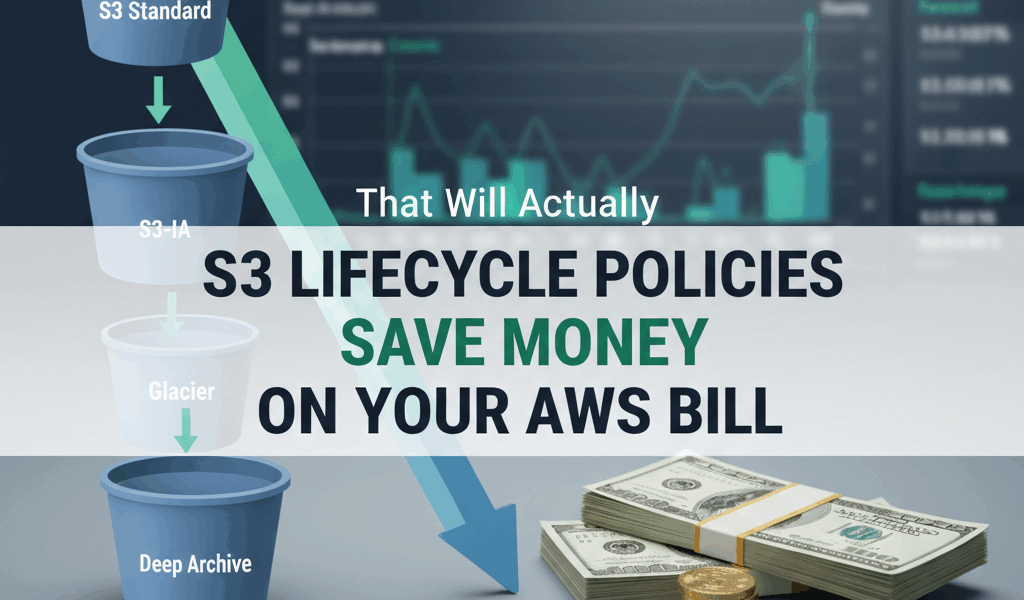
Some AWS services support resource-based policies that grant access directly to resources. S3 bucket policies, SQS queue policies, and Lambda function policies are probably the most common ones. These policies can grant cross-account access without needing role assumption, which simplifies some architectures but gives you less centralized control.
When you combine identity-based and resource-based policies, think it through carefully. Both have to allow the action for cross-account access when you’re using roles. For same-account access, either policy allowing it is enough. Make sure you document which resources have resource-based policies so you can actually keep track of everything.
Service Control Policies
If you’re using AWS Organizations, Service Control Policies give you guardrails across all your accounts. SCPs define the maximum available permissions for member accounts. Even your account administrators can’t exceed SCP limits. That’s what makes SCPs endearing to us security-minded folks – they’re the ultimate backstop that nobody can bypass.
Layer your SCPs thoughtfully though. If you put overly restrictive SCPs at the organization root, they affect all accounts. Use organizational units to apply different SCPs to different account groups. Your production accounts probably need stricter controls than your sandbox accounts.
Policy Validation and Testing
AWS IAM Access Analyzer validates policies against security best practices. You should integrate this validation into your CI/CD pipeline to catch overly permissive policies before they hit production. The analyzer identifies problems like wildcards in resource ARNs, unused permissions, and accidental public access.
Test your policies before you apply them to production principals. The IAM policy simulator lets you test how policies evaluate specific API actions. I usually create test roles with candidate policies and verify they allow what they should while denying inappropriate access.
Monitoring and Auditing
Enable CloudTrail in all regions and all accounts. Centralize the logs in a dedicated logging account that your application teams can’t modify. Then analyze those logs for unusual activity patterns – stuff like API calls from unexpected regions or attempts to access services that principal shouldn’t be touching.
Set up automated remediation for policy violations. AWS Config rules can detect non-compliant IAM configurations and trigger Lambda functions to fix them. Alert your security team when automatic remediation isn’t possible or when you see patterns that suggest someone’s account got compromised.
Review your IAM configurations quarterly. Get rid of unused roles, users, and access keys. Update policies to reflect what your applications actually need right now. This kind of IAM hygiene prevents privilege accumulation and keeps your attack surface smaller.
Getting good at IAM takes practice and continuous learning. Start with simple, restrictive policies and add permissions as you actually need them. Document your IAM design decisions and build up a library of well-tested policy patterns that work. Secure IAM is really the foundation that all your other cloud security controls depend on.



Leave a Reply